Home » Posts tagged 'Single-Sign-On (SSO)'
Tag Archives: Single-Sign-On (SSO)
Managing and Securing Employee’s Personal Devices (BYOD) through Active Directory 2012 R2 !
Now Managing of BYOD (Bring Your Own Device) through Microsoft Active Directory 2012 R2-
Few weeks back, I have published my blog “Microsoft Windows Server 2012 R2 Top 20 Released Features!” and two of important features are “Workplace Join” and “Multitenant VPN gateway“. Today, Lets discuss on these features in more detail.
As per Microsoft TechNet Article:
“One of the most prevalent IT industry trends at the moment is the proliferation of consumer devices in the workplace. Employees and partners want to access protected corporate data from their personal devices, from checking email to the consumption of advanced business applications. IT administrators in organizations, while wanting to enable this level of productivity, would like to continue to ensure that they can manage risk and govern the use of corporate resources.”
In Windows Server® 2012 R2, Active Directory has been enhanced with the below value propositions to connect employee’s personal devices to internal corporate network to access their application from anywhere anytime in a secured manner. It enables IT to empower their users to be productive from a variety of devices:
- Workplace Join – IT administrators can allow devices to be associated with the company’s Active Directory and use this association as a seamless second factor authentication.
- Single Sign-On (SSO) from devices that are associated with the company’s Active Directory
- Managing Risk – Enable users to connect to applications and services from anywhere with Web Application Proxy
- With Multi-Factor Access Control and Multi-Factor Authentication (MFA), manage the risk of users working from anywhere, accessing protected data from user’s devices.
Though “Workplace Join” feature is self-explanatory but let me explain here – Employee can “join” his/her own devices to his/her own “workplace” (Internal Corporate Application/Data). In simple terms, Employees can access their applications and data everywhere, on any device.
In this case, Employees require to registering their devices with their AD domain so that device will reflect in AD with associated owner and will be trusted when requesting and running company-secured applications, accessing company-secured data, or accessing company-secured resources.
To get more detail on Workplace Join – Join to Workplace from Any Device for SSO and Seamless Second Factor Authentication Across Company Applications Overview
When user joins a device to the workplace, it becomes “a known device and will provide seamless Second Factor Authentication and Single-Sign-On (SSO) to workplace resources and applications.” And once the device is “known”, IT Administrator can leverage that knowledge to apply/enforce additional configurations/policies (example: pushing company polices settings to the device). Administrators can control who has access to company resources based on application, user, device, and location.
Practically speaking, Device Registration Service (DRS) is the new feature and part of Active Directory Federation Service (ADFS) role which allows users to register their devices in AD Domain, tracks the associated device’s certificate in order to represent the device’s identity and provides on-board mechanism for Single Sign-On (SSO) with appropriate/conditional access.
Single Sign-On (SSO) is the functionality that reduces the number of password prompts the end user has to enter when accessing company resources from known devices. This implies that Users will be prompted only once during the lifetime of SSO when accessing company applications and resource. For example, A User wants to access their different applications (SharePoint, Exchange and HR) from their devices – without SSO, user would be prompted for a login with every application user try to access. But with SSO, user will only be asked one time.
As above mentioned, Device Registration Service part of ADFS role allows claims-based authentication to occur based on trusted certificates. Once the user is authenticated (username + password + trusted device along with certificate), the claim is trusted/validated, can be used to launch company applications or access company data.
To get more detail on Single Sign-On – Join to Workplace from Any Device for SSO and Seamless Second Factor Authentication Across Company Applications Overview or Single sign-on Wikipedia, the free encyclopedia
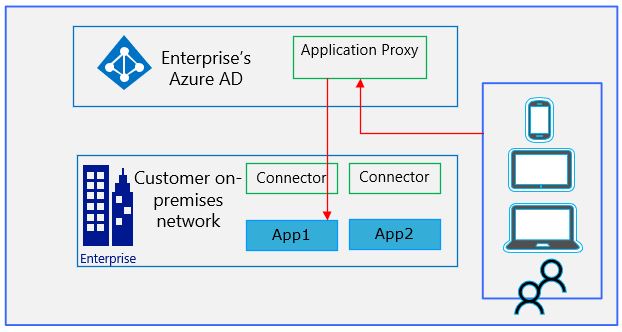
Managing Risk through Web Application Proxy:
The Web Application Proxy is a new service part of Remote Access Role. Web Application Proxy “provides reverse proxy functionality for web applications inside corporate network to allow users on any device to access them from outside the corporate network. It pre-authenticates access to web applications using ADFS, and also known as an ADFS proxy.”
So, now SSO facilitated through DRS, the authenticated AD user with his/her own device can access applications on the corporate network and manage the risk with a reverse proxy secure layer without having a 3rd party VPN connection.
To get more detail on Managing Risk through Web Application Proxy – Connect to Applications and Services from Anywhere with Web Application Proxy Overview
Multi-Factor Access Control and Multi-Factor Authentication (MFA):
ADFS in Windows Server 2012 R2 supports more than just the permitted (or denied) user in ADFS claims. Microsoft added “Multiple Factors Authentication”, including user, device, data and location. Authorization claim rules have a greater variety of claim types.
“In ADFS in Windows Server® 2012 R2, Administrator can enforce multi-factor access control based on user identity or group membership, network location, and device (whether it is workplace joined)”
To get more detail on Multi-Factor Access Control and Multi-Factor Authentication (MFA) – Manage Risk with Additional Multi-Factor Authentication for Sensitive Applications Overview