Microsoft Identity as a Service (IDaaS) for Enterprise Architects
“What IT architects need to know about designing Microsoft identity solution for customer while they deployed any public and private cloud (hybrid) with all types of cloud services such as IaaS, PaaS and SaaS“
Brief Introduction
In my previous article “Microsoft Azure AD Identity Solution – Part-1 !!!”, we discussed about Microsoft Azure AD as an identity solution in detail and how Azure identity (IDaaS) solution effectively address the challenges on seamless access & integration with a wide range of legacy apps and modern SaaS services in a multi-hybrid cloud environment such as AWS, Azure and Google cloud.
In this article, we will focus on some more industry use cases of Azure identify solution and its integration capabilities. These industry use cases are such as seamless solution on single sign-on (SSO) and multifactor authentication (MFA), Azure AD collaboration with business-to-business (B2B) partners and business-to-consumer (B2C) and then finally talk about Azure AD application proxy
Seamless SSO and MFA solution to SaaS and on-premise applications
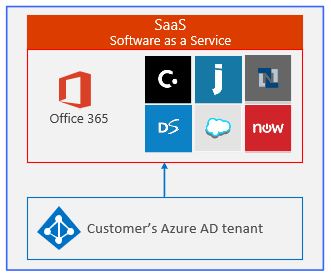
An Azure AD integration with hybrid cloud provides a seamless single sign-on (SSO) and multi-factor authentication (MFA) capability to SaaS and on-premises apps. Refer to the below figure on how Azure AD tenant connects to Azure SaaS apps such as office365, ServiceNow and others apps:
The seamless single sign-on of Azure AD tenant is the following:
- An emerging need of unified application access and single sign-on to all types of SaaS applications
- Consistent user experience with single sign-on across all SaaS services and on-premises apps by using below SSO methods:
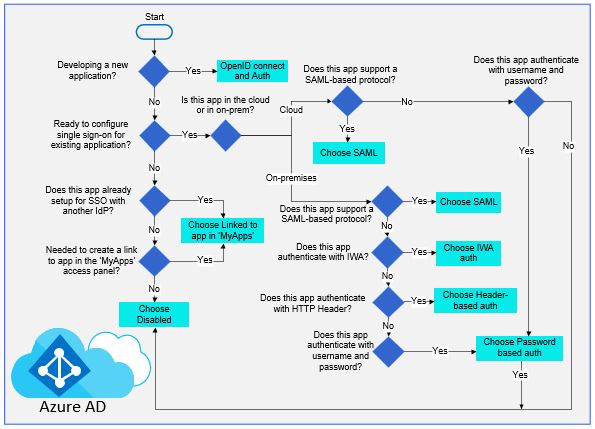
- Cloud SaaS apps can user Open-ID Connect, OAuth, SAML, password-based, linked or disabled methods for SSO
- On-Premises applications can use password-based, integrated windows authentication (IWA), header-based, linked or disabled methods for SSO. The on-premises choice works when applications are configured with application proxy
The following flowchart help Identity Architect to decide on which Azure AD single sign-on method is best for their business apps and fits in their business scenario:
A traditional enterprise SSO solution such as on-premises corporate AD can extend to SaaS services by using Active Directory Federation Services (ADFS).
The seamless multi-factor authentication (MFA) of Azure AD tenant covers below:
- A process where a user is prompted during the sign-in for an additional form of identification, such as to enter a code from their mobile phone or to provide a fingerprint scan.
- Customer on-premises applications or SaaS services don’t require to make any changes to use Azure MFA. The verification prompt is part of Azure AD sign-in event, that automatically request and processes the MFA challenge when needed.
- Azure MFA generally works by needing two or more methods:
- Password
- Trusted devices that is not easily duplicated (a phone or hardware key)
- Biometrics (a fingerprint or face scan)
Azure AD B2B and B2C collaboration
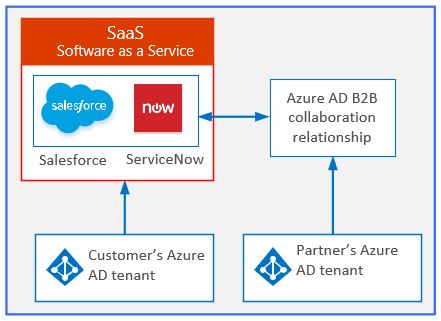
Azure AD B2B collaboration enables secure integration between business to business partners
These new capabilities make it easy for businesses to create advanced trust relationships with Azure AD tenants so they can easily share their business apps (such as ServiceNow, Salesforce etc.) across companies/customers without hassle of managing additional directories or having the overhead of managing partner’s identity solution.
Below figure shows how an Azure AD B2B collaborates with SaaS applications between customer’s and partner’s Azure AD tenant:
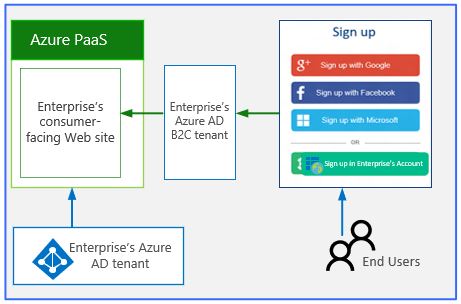
An Azure AD B2C is a highly available, global, identity management service for consumer-facing applications that scales to hundreds of millions of identities.
An Azure AD B2C easily integrates across mobile and web platforms, through this consumers login to all their apps through fully customizable experience by using their existing social accounts such as Google, Facebook, Linked-In or by creating new credentials. Below figure shows how an enterprise Azure AD B2C collaborates with Azure PaaS through consumers social identities:
Azure AD application proxy
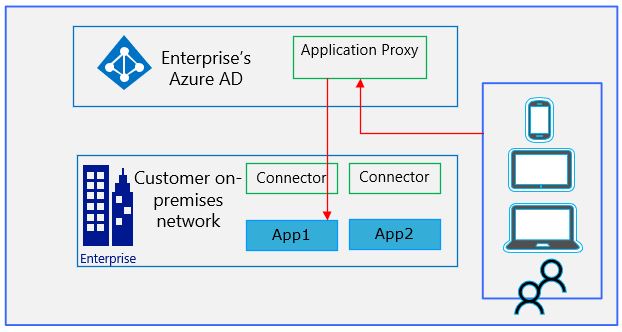
Microsoft Azure AD application proxy lets customer publishes their web-based apps inside their private network and provides secure access to users outside world as below:
- Employees can log into their apps from home on their own devices and authenticate through this Azure AD cloud-based proxy
- By using Azure AD proxy customer also can protect their on-premises apps with the same requirements as other cloud-based apps with MFA, and other conditional access.
- Application proxy works by installing a slim Windows service called “Connector” inside a private network and that maintains an outbound connection from within private network to this Azure AD proxy service
Below figure shows how an on-premises application can be accessed through an Azure AD application proxy.
To have further more insight on my previous article on “Microsoft Azure AD Identity Solution – Part-1 !!!” , Refer to below article:
Microsoft Azure AD Identity Solution – Part-1 !!!
Rajeev Ujjwal has more than 18 years of transformation delivery experience in cloud computing, infrastructure, directory service, and cyber security with larger global customers. He is a senior cloud consultant and successfully delivered various kind of global project delivery such as greenfield, consolidation, separation and migration.
